External Attack Surface Management
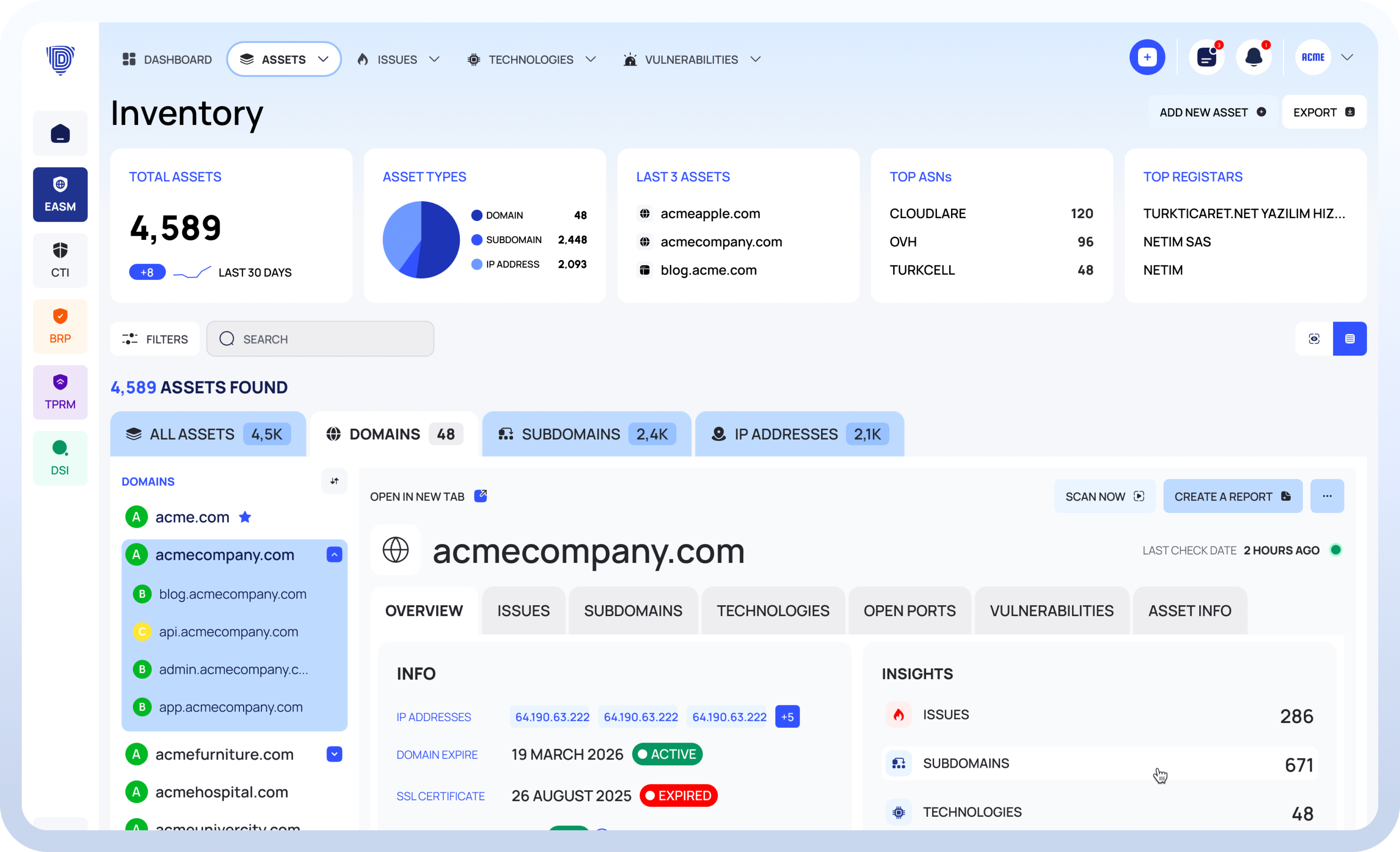
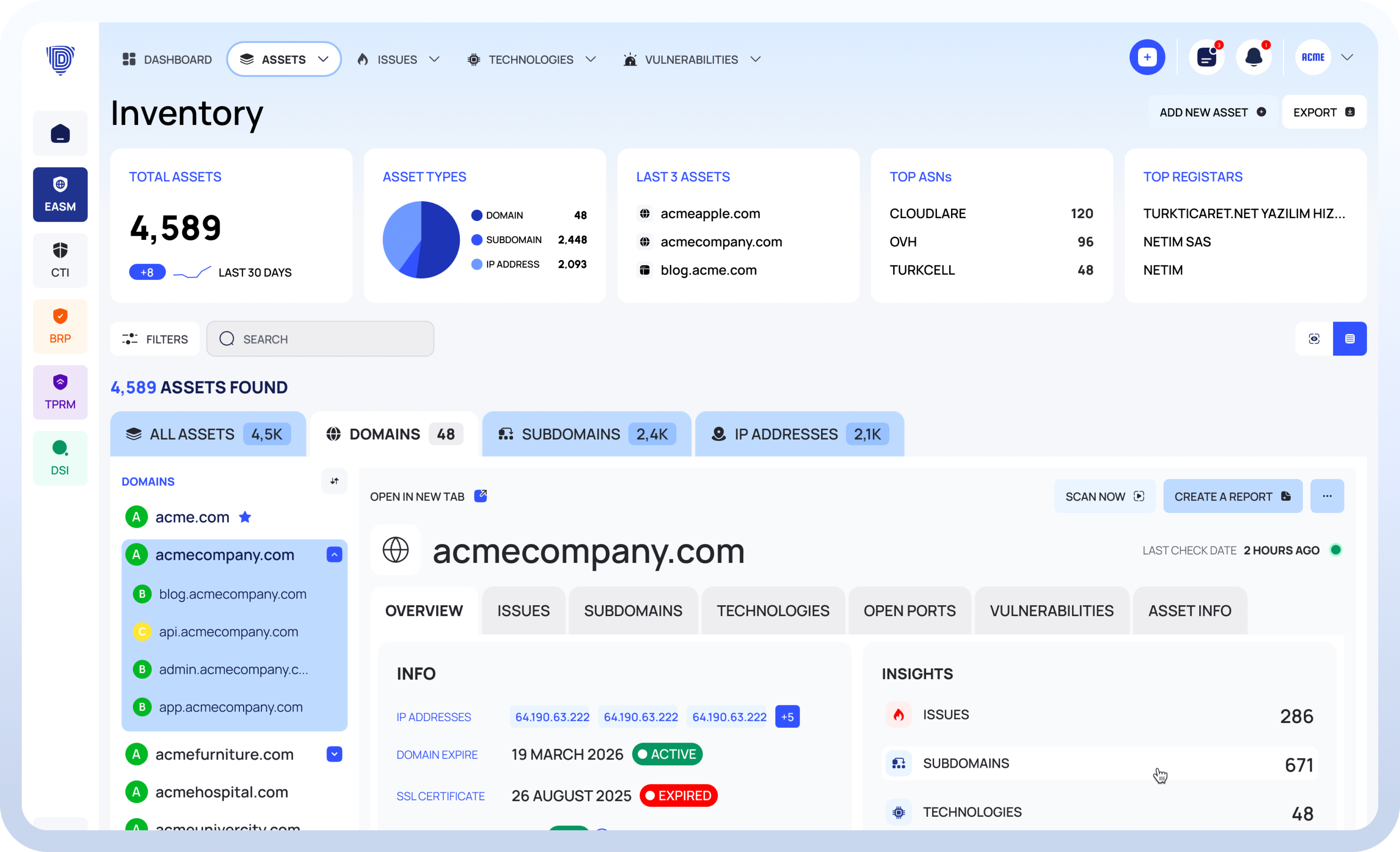
Discover Every Internet-Facing Asset
Continuously Scan and Store Asset Data
Detect Issues, Misconfigurations, and Vulnerabilities
Search Your Assets with Advanced Filters
Prioritize with Daily Risk Scores
Investigate Issues with Guidance and Proof
Reports
Produce detailed reports tailored to different audiences: asset inventory reports for security analysts, technology reports for IT infrastructure teams, and executive summary reports for leadership and board communication. Reports reflect the current state of your attack surface with scoring, issue breakdowns, and trend data. Share them internally or use them for compliance documentation and audit readiness.
Notifications
Configure notification rules to match your operational needs. Receive alerts when a new asset is discovered, when an asset's risk score drops below a defined threshold, when a new vulnerability is detected, or when key configurations change. Notifications can be customized by severity, asset group, or issue type so your team gets relevant signals without noise.
APIs
Work directly in the Deepinfo Platform for full visibility through dashboards, search, and reporting. Or integrate the same capabilities into your existing workflows through comprehensive APIs. Query assets, pull historical scan data, retrieve risk scores, or automate report generation. Both paths deliver the same continuous intelligence.
See Your Entire Attack Surface.
Trusted by leading companies worldwide, the Deepinfo Security Platform is the preferred choice for continuously managing cyber threat exposure.